If your IT was breached tomorrow,
could you prove your cyber insurer should pay?
Most policies are a fiction until you can evidence them. We pressure-test yours line-by-line, using the exact attack vectors a loss adjuster uses, before the day your claim depends on it.
12-minute diagnostic · Free · No credit card · Output is yours to keep
Hartley & Sons Engineering Ltd
Fixable - but far easier to fix before a claim lands than during one.

Three sentences that have killed
more cyber claims than any breach.
Every cyber policy contains promises you've made. Can you evidence every one of them? Below, three of the most common - and what your insurer actually checks when a claim opens.
“MFA enforced
for every user account.”
94% of users covered. Six senior accounts are on a six-month grace period - including your finance director and your CEO's PA.
“Backups are
tested regularly.”
A full restore was last attempted 14 months ago. Your insurer's policy schedule asks for evidence within the last 90 days.
“Documented
incident response plan.”
A Word document downloaded from a template site in April 2019. Nobody has opened it in 18 months. It names a CISO who left the business in 2022.
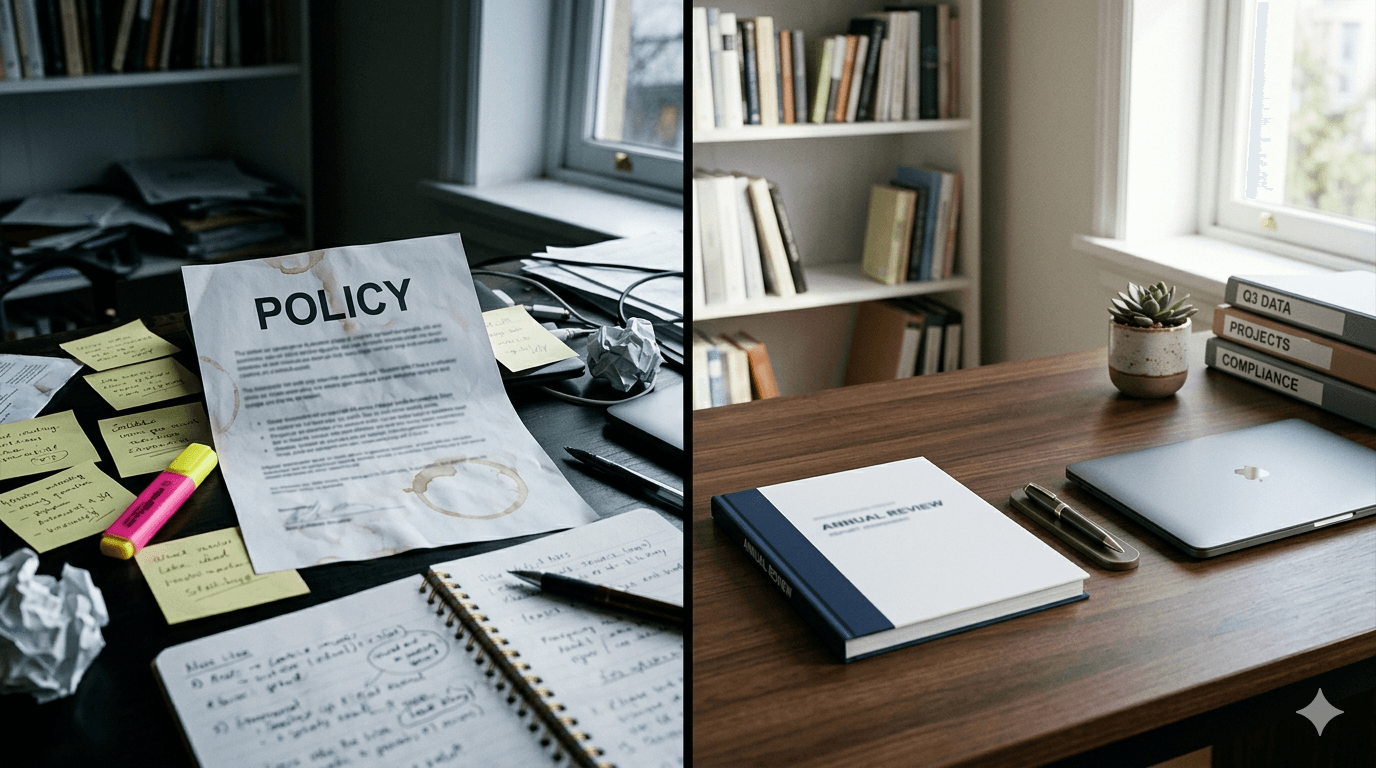
These aren't security failures. They are evidence failures.They're the difference between a policy that pays and one that doesn't.
Already convinced? Fixed-price review. Results in 5 working days.
Start the Review — £950Refund if no meaningful proof gaps found.From “we think we're covered”
to “we can prove it.”
Senior-human-led. Evidence-first. Each move ends with something:
Yours to keep, even if you walk away.
A signed claim-defensibility report
In 12 working days. Layered like the loss adjuster's own thinking. Yours to keep.
An owned-gap map
Every gap named, severity-rated, and assigned. No more “we thought IT had that.”
A 30-minute board readout
Plain English. No jargon. The conversation you've been avoiding - defended.
Your sector. Your wording.
Your insurer's exclusions.
Tender qualifications. Cyber claims. FCA reviews. Customer security questionnaires. Each sector has its own language and its own evidence bar.
Can we pass the security section of this main-contractor questionnaire — honestly?
Construction supply chain runs on PQQ answers. One unanswerable evidence question can move you down the preferred-supplier list. Axulu builds the evidence pack once, then keeps it current — so every tender uses the same defensible truth.
Axulu can provide 5 layers of defensibility.
Each layer solves a different evidence gap. Start where the claim risk is highest.
Axulu Safe
“Can you prove your claim should pay?” Cyber Liability Protection. Evidence-mapped to your policy, ready for the worst day.
Learn more →Titanium
“Stop firefighting your own estate.” Hardened, standardised, recoverable. The operating base evidence is built on.
Learn more →Axulu Plan
“See what's coming. Decide deliberately.” The 7 Year Plan. Cost, risk, and certification plotted on one canvas.
Learn more →Supercharge
“Use AI without losing control.” Tailored AI & automation. Practical leverage, governed, role-shaped.
Learn more →Expert Leadership
“CIO-level thinking, without the hire.” Fractional CIO / CTO / Head of Architecture. The human judgement behind the outcomes.
Learn more →Common questions
Aren't you just another MSP?
The Axulu service Titanium looks a bit like an MSP - in the same way a locksmith and an insurance loss adjuster both think about break-ins. But one installs the locks. The other decides whether your claim pays out when somebody gets past them.
I know the difference because I built the locksmith. Ten years running an MSP, grown organically and by acquisition to £12m revenue and 96 staff across the UK. What I learnt the hard way: business owners don't actually want tech. They want two outcomes - that the business keeps running even when the tech doesn't, and that when (not if) they're breached, the regulator and the insurer don't add liability on top of the disruption.
So I built Axulu from the ground up as a Cyber Liability Protection service. Sometimes that means we provide the protected IT underneath. Sometimes it's just expert human governance sitting on top of your current IT company. Either way, the outcome is the same: you sleep at night.
How is Axulu different from my IT provider?
Your MSP runs your tickets and tools. Axulu runs your evidence. MSPs are paid to fix things; we're paid to prove the things that were true on the day a breach started. We don't compete with your MSP - we sit above them and make sure the controls they implement actually satisfy your insurer, your auditors, and your board.
CIO-level thinking,
without the £180k hire.

“When the insurer interrogates your claim, you need someone who has already built the evidence file.”
Matthew White - Principal & founder
30 years across enterprise architecture, M&A integration, cyber policy interpretation, and vCIO work. When the insurer interrogates your claim, you need someone who has already built the evidence file - not a script, not a checklist, not a junior in a suit. Every Axulu engagement starts there.
Choose your next move
Find the proof gap, keep it current, or build the system properly.
Start with a fixed-price review, move into continuous proof management, or scope a 30-day framework-readiness sprint when scrutiny is already approaching.
Find the Gap
Framework-Ready Review- Results in 5 working days
- Board-ready summary included
- Refund if no meaningful proof gaps found
Stay Defensible
ProofOps™- Monthly evidence review
- Quarterly readiness assessment
- Limited onboarding slots
Get Framework-Ready
Framework-Ready Sprint™- 30-day intensive programme
- Executive-ready outputs
- Selected projects only
Frequently asked.
What boards, MDs, and finance directors ask before signing.
Aren't you just another MSP / IT support company?
The Axulu service Titanium looks a bit like an MSP - in the same way a locksmith and an insurance loss adjuster both think about break-ins. But one installs the locks. The other decides whether your claim pays out when somebody gets past them.
I know the difference because I built the locksmith. Ten years running an MSP, grown organically and by acquisition to £12m revenue and 96 staff across the UK. What I learnt the hard way: business owners don't actually want tech. They want two outcomes - that the business keeps running even when the tech doesn't, and that when (not if) they're breached, the regulator and the insurer don't add liability on top of the disruption.
So I built Axulu from the ground up as a Cyber Liability Protection service. Sometimes that means we provide the protected IT underneath. Sometimes it's just expert human governance sitting on top of your current IT company. Either way, the outcome is the same: you sleep at night.
Isn't this just consulting dressed up as software?
How is Axulu different from my MSP?
Do you sell cyber insurance?
The 18% Vulnerable score in your demo - is that representative?
What does “evidence-sensitive SME” mean?
What if my environment is a mess?
Who reviews our policy?
What if our data is sensitive?
 CIOCTOARCH
CIOCTOARCHYour next renewal deserves a defensible answer.
12 minutes. Free. Senior-led. You'll walk away knowing exactly where you stand.
No credit card · Senior architect on the call · Outputs yours to keep